Randy Arendell is Partner Success Director at CHeKT, guiding dealer engagement and partner growth. In this guest expert blog, Randy breaks down the financial toll of false alarms, why traditional systems falter, and how AI-driven verification is revolutionizing security detection, response, and trust.
The professional monitoring industry is at a tipping point. Artificial intelligence and cloud-based services are fundamentally reshaping how operators, central stations, and security integrators deliver safety, efficiency, and intelligence at scale. As technology evolves, one challenge has become impossible to ignore: false alarms.
The True Cost of False Alarms
False alarms affect everyone in the chain. They waste operator time, frustrate customers, create costly fines, and erode trust in the entire system. Studies show that up to 98% of all alarms are false, representing more than $1.8 billion in annual losses across the United States.
Every false signal consumes resources that could be directed toward real threats. It also delays emergency response times, creating a ripple effect that impacts both safety and confidence.
Why False Alarms Happen
Traditional alarm systems were designed around simple binary signals: a door opens, glass breaks, motion is detected, an alarm triggers. What these systems lack is context. Operators are forced to decide, often within seconds, whether an event is real or not, with very little information.
Common culprits include:
- A spider crossing a night-vision lens
- Headlights reflecting off a wall
- Wind, rain, or moving shadows
- Authorized workers or cleaning crews moving after hours
Without visual context or intelligent filtering, systems treat all motion the same. The result is alarm fatigue for operators and mistrust from end users.
How AI Redefines Detection
Artificial intelligence has changed the landscape by adding intelligence to the signal chain. Instead of reacting to every motion or pixel change, AI-powered detection focuses only on what matters such as people, vehicles, or unusual motion within a defined zone.
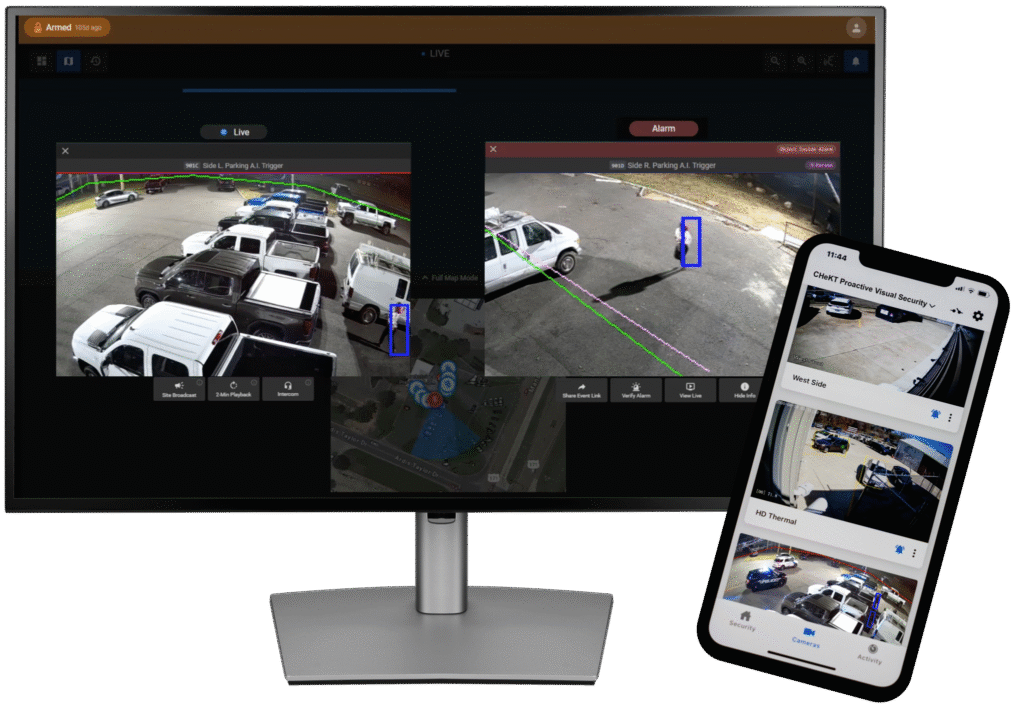
Modern systems layer AI at multiple levels:
- Edge Analytics: Smart cameras or NVRs detect motion and classify objects locally, reducing bandwidth and initial noise.
- Cloud Verification: Detected objects are verified in the cloud, filtering out irrelevant triggers such as headlights, animals, or blowing debris.
- Site Policies: Intelligent rules determine when and how to escalate alerts, such as after-hours movement, restricted zones, or repeated behavior patterns.
This combination of localized analytics and cloud validation delivers both accuracy and scale. Operators see fewer nuisance events, and when alerts do occur, they are far more likely to represent genuine threats.
Real-World Scenarios
AI-driven monitoring is not theoretical. It is reshaping the way security operations centers function every day.
- After-Hours Retail Storefront: A camera detects movement near a glass entry. Cloud AI confirms it is a person, not passing headlights. Operators issue a deterrent message, and the subject leaves without incident.
- Distribution Yard: Vehicle detections are logged during business hours but only escalated if a vehicle enters a restricted zone or idles too long.
- School Campus: Policies shift by schedule. What is acceptable during the day becomes a monitored event after hours. AI ensures that late-night loitering is flagged immediately.
- Office Buildings: Cameras distinguish between cleaning crews and unauthorized entry, allowing property managers to focus only on unexpected activity.
These examples demonstrate how layered intelligence can dramatically reduce false alarms while improving situational awareness.
The New End-to-End Event Flow
A modern event chain now looks like this:
- Detection: A person enters a defined area; the camera’s analytics recognize motion.
- AI Verification: The system confirms a human presence and filters out irrelevant triggers.
- Policy Application: Business rules determine whether to escalate, log, or ignore the event.
- Operator Response: A short video clip and clear timeline give operators immediate context.
- Outcome: Faster, smarter response, with verified video leading to quicker intervention and improved law enforcement outcomes.
The Road Ahead
As the security industry embraces AI and cloud technologies, the path forward is clear: fewer false alarms, more meaningful alerts, and greater confidence at every level.
The shift from reactive monitoring to proactive visual security marks one of the most important transformations in decades. Operators, integrators, and central stations who adapt to this new model will not only save time and resources, they will redefine what true protection means in a connected, intelligent world.
Turning Intelligence into Action
Modern security is no longer just about detection; it is about verification and response. AI-powered, video-verified solutions connect cameras, analytics, and monitoring operators into one unified workflow, ensuring that every alert is supported by visual context and real-time intelligence. The result is fewer false alarms, faster police response, and a higher level of trust between the client, the integrator, and the monitoring center.
If you’re interested in learning more about how AI-powered video verification can strengthen your monitoring operations and reduce false alarms, reach out to our team or our partners at CHeKT today to start the conversation.